⚠️ Privacy Notice
This case study is based on a real investigation conducted by HawkEyes OSINT Tools and Services. However, all addresses, transaction hashes, amounts, dates, and other identifying details have been fictionalized to protect client privacy and maintain confidentiality. The methodologies and investigative techniques described are authentic and represent our actual capabilities in cryptocurrency tracing and blockchain analysis.
🔍 Introduction
This investigation demonstrates advanced cryptocurrency tracing techniques used to follow stolen funds through multiple blockchain networks and exchanges. The case involved tracing 3.569 Bitcoin through various intermediary addresses, privacy-focused exchanges, and cross-chain swaps, ultimately identifying deposits at major KYC-compliant exchanges. This comprehensive analysis showcases the methodologies employed in modern cryptocurrency investigations and the challenges faced when dealing with sophisticated money laundering schemes.
📋 Assignment Overview
The client provided 18 cryptocurrency transaction hashes, showing a total transfer of 3.569 Bitcoin (BTC) to an address identified as belonging to Crypto CVM. When the client attempted to withdraw funds from Crypto CVM, the request was denied, leading to suspicions of fraud via a fake investment website. HawkEyes was engaged to trace the alleged stolen funds and determine if they could be tracked to Know Your Client (KYC) compliant cryptocurrency exchanges.
Tools utilized: Breadcrumbs, Arkham Intelligence, and Bitquery for comprehensive blockchain analysis.
📊 Results Summary
The investigation successfully traced the stolen cryptocurrency funds from initial client deposits through various intermediary addresses and services, including privacy-focused exchanges like ChangeNow and ThorChain, ultimately leading to deposits at major exchanges including Binance and OKX. The analysis revealed sophisticated money laundering patterns involving currency conversions from Bitcoin to Ethereum and Tether, demonstrating the complexity of modern cryptocurrency fraud schemes.
💰 Initial Deposit Analysis
Between February 15, 2024, and May 22, 2024, the client made 18 BTC transfers from various Kraken addresses to the suspected scammer's wallet. Analysis of the transaction patterns revealed that the CVM wallet was first active in January 2024 and continued operations through late May 2024. Each client deposit was quickly moved to intermediary addresses, typically within several days, indicating an organized operation.
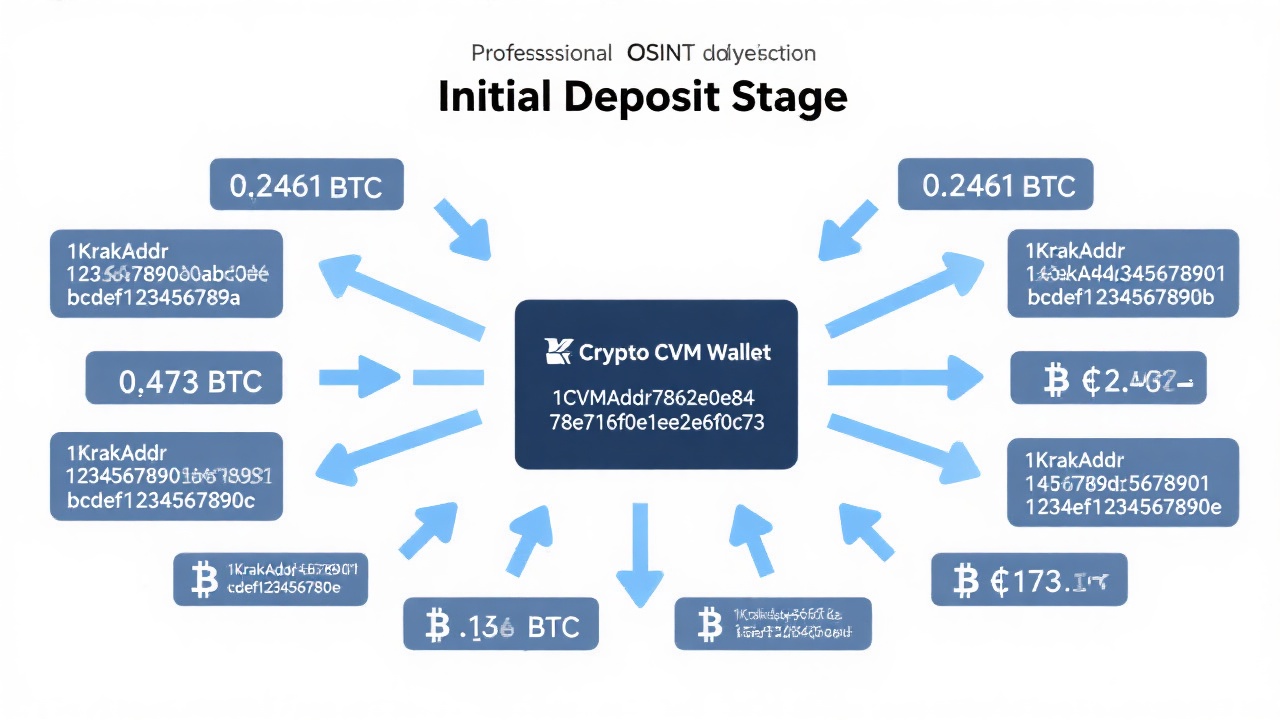
Figure 1: Initial deposit flow from multiple Kraken addresses to CVM wallet - For illustration purposes only, addresses have been fictionalized
🏦 Stage 1: February 8 - March 1 → Binance Route
The first traced funds, deposited on February 6, 2024 (0.2461 BTC), followed a clear path through two intermediary addresses before reaching a Binance deposit address. The funds were combined with additional deposits and systematically moved through the network, with 91% of outgoing transactions from the intermediary addresses flowing to either other connected addresses or the identified Binance deposit address.
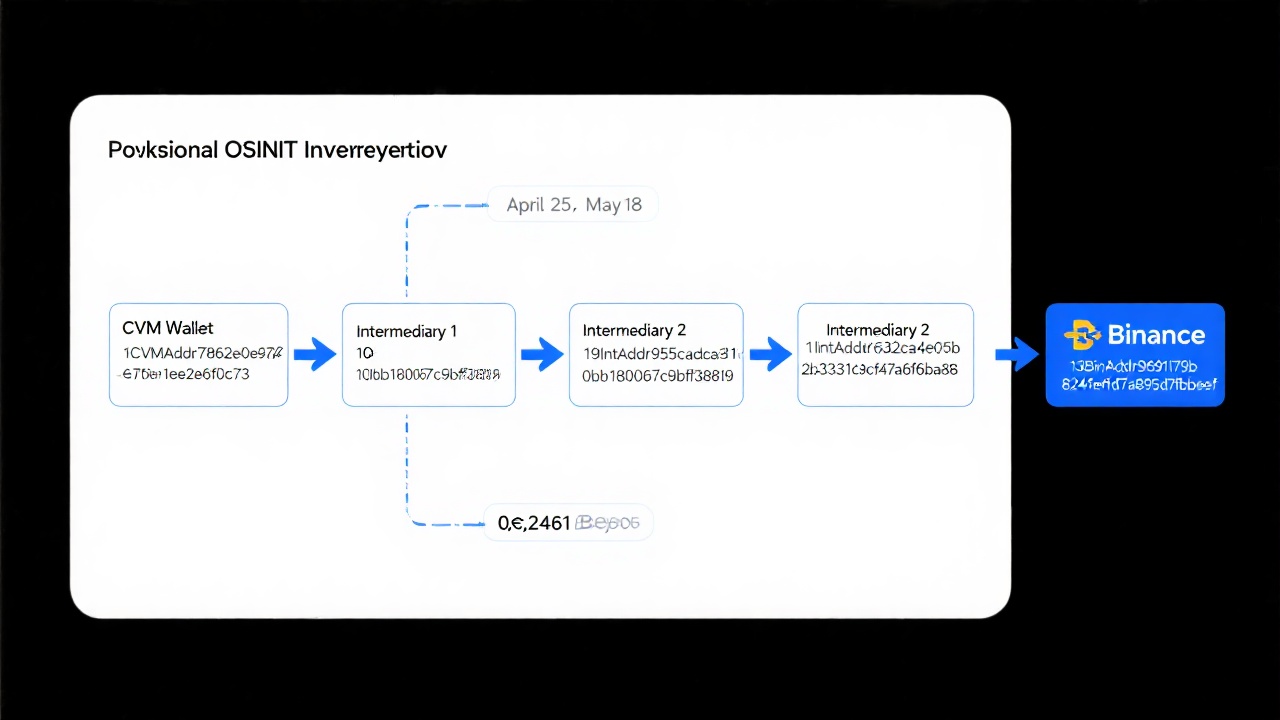
Figure 2: Fund flow from CVM wallet to Binance through intermediary addresses - Diagram for illustration purposes only
🔄 Stage 2: March - April → ChangeNow to Multiple Exchanges
Funds deposited after March 15th followed a more complex route through ChangeNow, a cryptocurrency exchange service that allows users to exchange currencies without account creation or identity verification. The investigation identified 13 separate transactions to ChangeNow deposit addresses, with amounts ranging from $9.5K-$9.8K in March to $18.5K-$18.8K in early April.
Pattern Analysis: The deposits into ChangeNow followed a deliberate pattern showing clear intent to disguise the flow of funds. Large amounts were systematically broken down into multiple smaller transactions spread over several weeks. This fragmentation technique is a common money laundering tactic designed to avoid detection thresholds and create confusion in the transaction trail. The consistent timing intervals and amount variations demonstrated sophisticated planning rather than random transaction behavior.
Through correlation analysis with Arkham Intelligence data, the team identified a pattern where BTC deposits to ChangeNow were converted to USDT and sent to a Tron network address. These funds were subsequently split between multiple paths, with portions reaching both OKX and Binance deposit addresses.
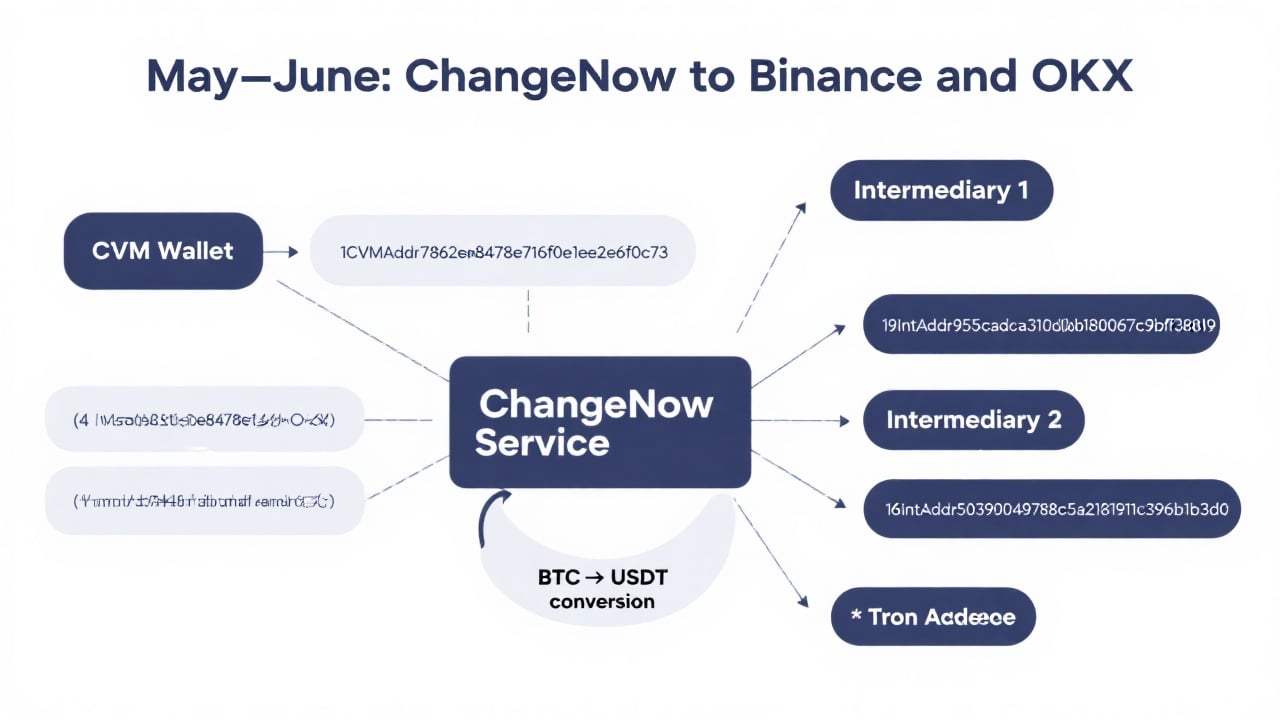
Figure 3: Complex routing through ChangeNow service with currency conversion - Simplified diagram for illustration purposes
⛓️ Stage 3: April - May → ThorChain Cross-Chain Swaps
The final stage involved the use of ThorChain, a decentralized exchange protocol enabling cross-chain cryptocurrency swaps without requiring user accounts. Client deposits totaling 1.526 BTC were processed through ThorChain Vaults in four separate transactions of approximately one Bitcoin each between April 27 - May 2, 2024.
The investigation tracked these funds across blockchain networks, identifying conversions to both USDT (41K and 63.4K amounts) and Ethereum (3.72, 17.2, and 19 ETH amounts), all ultimately deposited into OKX exchange addresses on different networks.
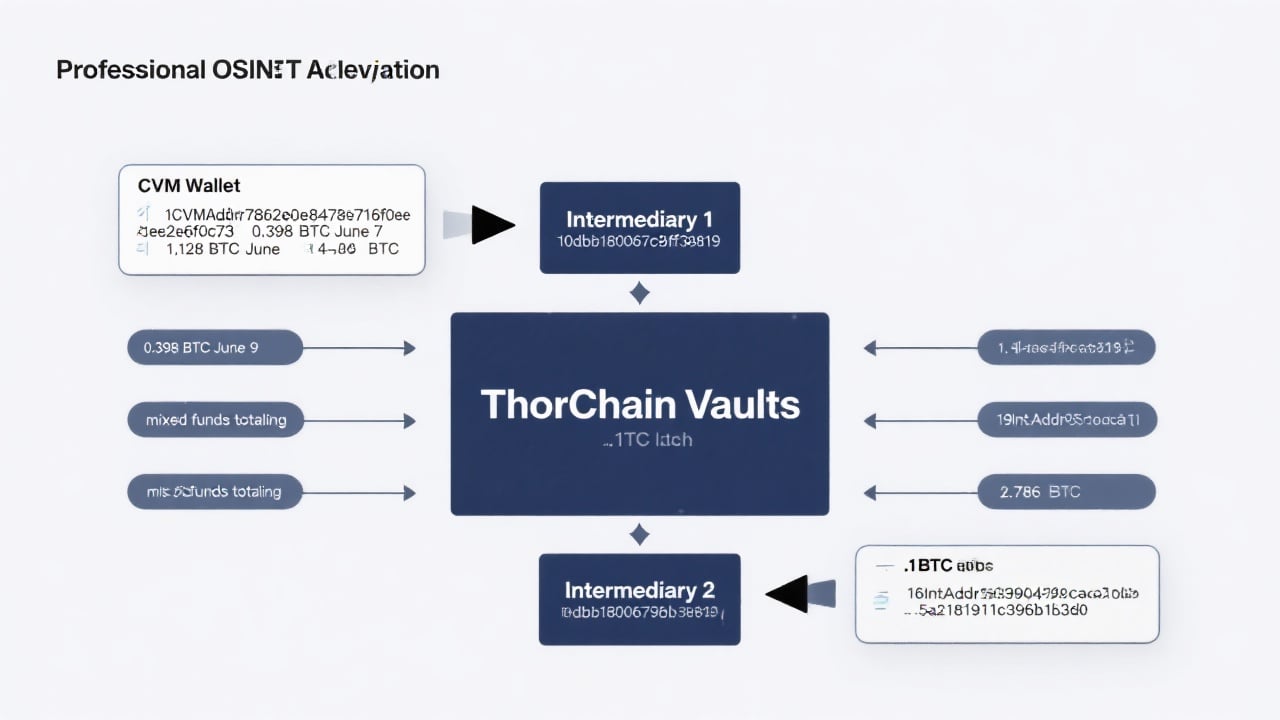
Figure 4: Cross-chain routing through ThorChain to OKX deposits - Conceptual diagram for illustration purposes only
🔗 Technical Analysis Methodology
The investigation employed several advanced techniques:
- Address Clustering: Identifying related addresses through transaction pattern analysis and timing correlations
- Exchange Attribution: Utilizing Arkham Intelligence's labeled address database to identify exchange deposit addresses
- Cross-Chain Tracking: Following funds across Bitcoin, Ethereum, and Tron networks through bridge services
- Temporal Analysis: Correlating transaction timing to establish fund flow relationships
- Volume Correlation: Matching input and output amounts across different services to confirm fund paths
- Pattern Recognition: Identifying deliberate fragmentation and timing patterns indicative of money laundering activities
📈 Key Findings
The investigation revealed several critical insights:
- 100% of client funds were successfully traced through multiple intermediary services
- Funds reached at least two major KYC-compliant exchanges (Binance and OKX)
- The operation utilized sophisticated money laundering techniques including privacy coins, cross-chain swaps, and non-KYC exchanges
- Strong address clustering evidence suggests all intermediary addresses belong to the same entity
- The scammer's operation was active for approximately 5 months with consistent patterns
- Deliberate transaction fragmentation patterns indicated sophisticated planning and intent to evade detection
⚖️ Conclusion
This investigation demonstrates the effectiveness of advanced blockchain analysis techniques in tracing cryptocurrency through sophisticated money laundering schemes. Despite the use of privacy-focused exchanges, deliberate transaction fragmentation, and cross-chain swaps, the systematic approach combining multiple analysis tools and methodologies successfully tracked the stolen funds to KYC-compliant exchanges, providing a solid foundation for potential recovery efforts.
The case highlights the importance of comprehensive blockchain analysis in cryptocurrency investigations and showcases how modern OSINT techniques can overcome traditional privacy barriers in digital asset tracing, even when facing deliberate obfuscation tactics.
📞 Contact Information
For questions about this investigation methodology or to discuss similar cryptocurrency tracing services, please contact HawkEyes OSINT Tools and Services via email: customer_service@hawk-eyes.io